Why FFT Perimeter Intrusion Solutions Are Essential for Effective Surveillance
Why FFT Perimeter Intrusion Solutions Are Essential for Effective Surveillance
Blog Article
Understanding the Relevance of Data and Network Safety in Today's Digital Age
In an age where digital transformation is important to company success, the significance of information and network safety has never been much more pronounced. Comprehending the consequences of data violations, along with the necessary security procedures needed to minimize these dangers, ends up being important.
The Surge of Cyber Dangers
The landscape of electronic protection has ended up being increasingly treacherous as cyber threats proliferate globally. Organizations across various fields are dealing with a rise in innovative assaults, ranging from ransomware to phishing systems. These threats not only compromise sensitive data but also interrupt organization procedures, leading to significant monetary losses and reputational damage.
Moreover, the introduction of innovative techniques such as man-made knowledge and machine discovering has furnished aggressors with the tools to automate their procedures, making it increasingly testing for standard safety procedures to maintain speed. As services navigate this treacherous landscape, the urgency for robust information and network protection approaches has actually never ever been higher, highlighting the demand for alert tracking, timely updates, and employee recognition to minimize these intensifying risks.
Consequences of Data Violations
Information breaches can have significant and severe implications for companies, impacting not only their economic standing yet likewise their trustworthiness and consumer trust. When sensitive information is jeopardized, companies typically face straight economic losses as a result of legal costs, regulatory penalties, and the prices linked with incident reaction. Additionally, the long-lasting impacts can be much more destructive; a ruined reputation may cause shed service opportunities and decreasing client retention.
The disintegration of client trust is possibly one of the most perilous effect of a data violation. Clients may wonder about an organization's capacity to secure their individual info and, therefore, may select to take their company somewhere else. This loss of confidence can cause lowered income and market share.
Furthermore, companies may experience boosted scrutiny from regulators and stakeholders, leading to a much more challenging functional environment. The psychological effect on employees, that might feel less protected or valued, can also impact efficiency and spirits.
Vital Safety Procedures
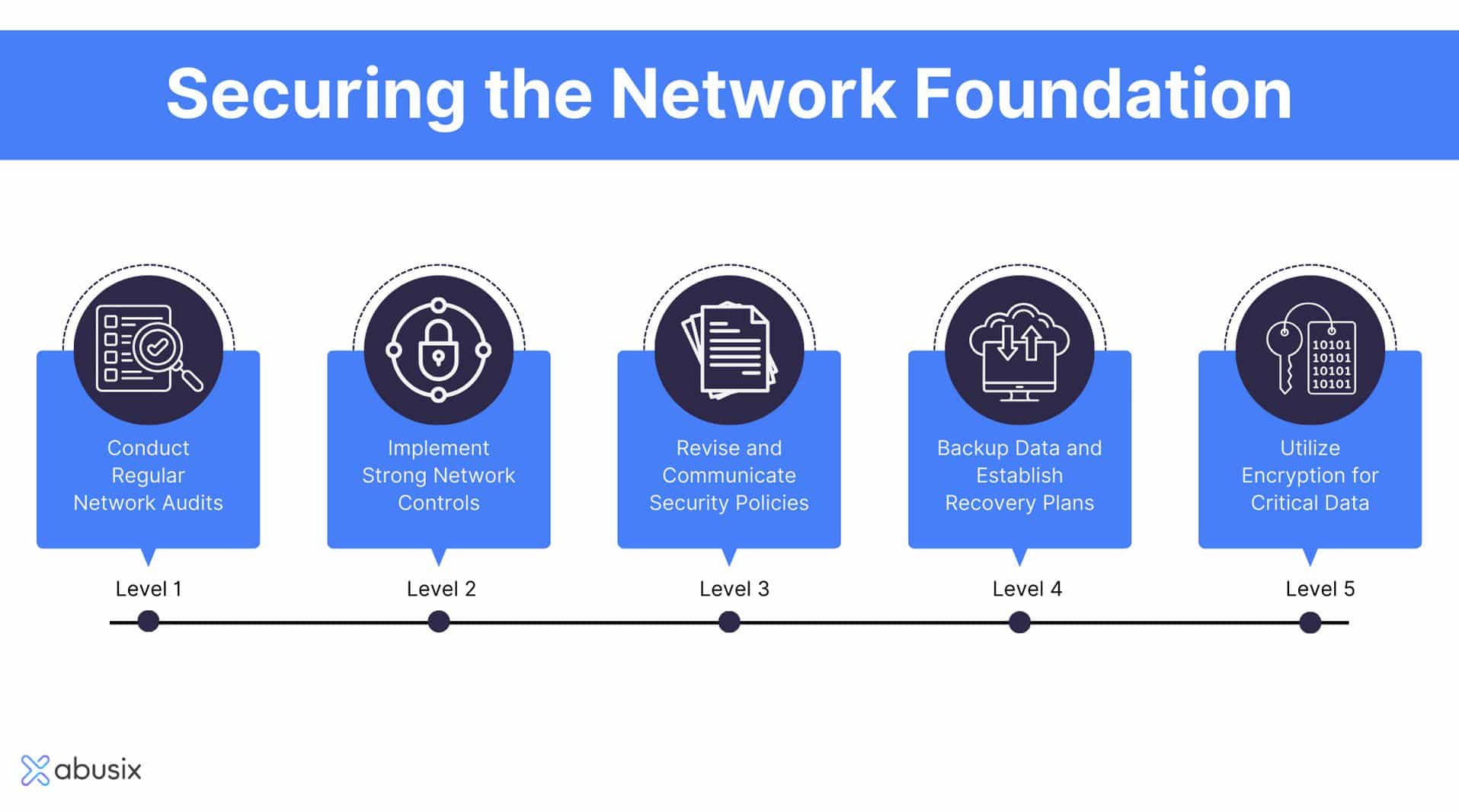
Implementing essential protection procedures is essential for safeguarding delicate details and preserving organizational stability. Organizations must embrace a multi-layered security technique that encompasses both digital and physical safeguards.
Among the foundational steps is to develop robust access controls, making sure that only licensed employees can access delicate information. This can be achieved with solid password policies, multi-factor authentication, and routine audits of user gain access to civil liberties. Additionally, securing data both en route and at remainder supplies a crucial layer of security against unapproved accessibility.
Routine software updates and patch administration are likewise vital, as they help alleviate susceptabilities that might be manipulated by malicious stars. Organizations should apply firewall softwares and intrusion discovery systems to monitor network traffic and identify possible dangers proactively.
Moreover, conducting routine safety evaluations and infiltration screening allows companies to identify weaknesses in their defenses before they can be exploited. Employee training on safety recognition is just as important, as click this link human error continues to be one of the leading causes of data violations. By incorporating these vital safety procedures, companies can dramatically reduce their danger exposure and enhance their resilience versus cyber threats.
Building a Safety And Security Culture
Creating an effective security society within a company is a crucial complement to executing durable security procedures. A protection society cultivates an environment where workers understand the importance of shielding sensitive info and are proactively involved in securing it. This culture is grown with comprehensive training programs that emphasize the relevance of data safety and security and the potential threats connected with carelessness.
Leadership plays a vital role in developing this culture. Staff members are more most likely to adopt comparable attitudes when execs prioritize protection and show their commitment. Routine interaction concerning safety and security updates, policies, and treatments makes certain that everyone stays alert and enlightened
Motivating open dialogue regarding safety concerns equips staff members to report suspicious tasks without concern of retribution. Carrying out an incentives system for proactive actions can further incentivize individuals to take possession of protection practices.
Additionally, performing drills and simulations aids reinforce the value of readiness and action. By incorporating protection into decision-making Click Here procedures and day-to-day procedures, companies can create a resilient workforce capable of adapting to progressing dangers. Inevitably, a solid security society not just shields information yet additionally boosts total business stability and reliability.
Future Trends in Information Safety And Security
Arising technologies and developing cyber dangers are reshaping the landscape of data protection, motivating companies to adapt their techniques appropriately. One significant pattern is the boosted adoption of synthetic knowledge (AI) and artificial intelligence (ML) for threat discovery and reaction. These modern technologies allow more aggressive safety steps by analyzing substantial quantities of data to recognize anomalies and potential violations in real-time.
Another fad is the relocation in the direction of zero-trust safety models, which run under the principle that no customer or tool must be relied on by default. This method stresses continual confirmation and decreases access to delicate data based upon strict verification processes.
Furthermore, the increase of remote job has increased the requirement for robust endpoint protection services that shield devices outside typical network boundaries - data and network security. As organizations accept cloud computer, protecting information en route and at rest has become vital, leading to the advancement of innovative encryption techniques
Verdict
Finally, the value of data and network safety can not be overemphasized in the contemporary digital landscape. As cyber hazards proceed to rise, important source organizations should continue to be watchful and positive in applying thorough safety and security steps. The possible effects of information breaches underscore the requirement of securing delicate info. Growing a society of safety recognition and adjusting to emerging fads will boost strength versus evolving cyber risks, eventually guaranteeing the security of valuable properties and keeping stakeholder trust fund.
In an era where digital transformation is important to company success, the importance of information and network protection has never been extra noticable. Recognizing the consequences of data violations, alongside the crucial protection steps needed to alleviate these risks, becomes crucial.Creating a reliable protection culture within a company is an important enhance to executing durable safety and security actions.Developing and arising technologies cyber hazards are reshaping the landscape of information safety and security, motivating organizations to adjust their techniques as necessary.In final thought, the importance of information and network safety and security can not be overstated in the contemporary digital landscape.
Report this page